Download and Install ZTE Axon 7 B35 Update [Android 7.1.1 Nougat]
ZTE is now rolling out another software update for its Axon 7 with December Security patch, KRACK, and Blueborne fixes. Follow this guide to download and install ZTE Axon 7 B35 update right […]
ZTE is now rolling out another software update for its Axon 7 with December Security patch, KRACK, and Blueborne fixes. Follow this guide to download and install ZTE Axon 7 B35 update right now.
Advertisement
The Axon 7 was announced back in 2016 and came with Marshmallow 6.0.1 out-of-the-box. While OEMs are solely focusing their attention on Android Oreo, ZTE seems to be a little late to follow up. The company has already launched the Oreo Beta program for the device. For now, the manufacturer has pushed a Security Maintenance Release (SMR) for the users. The update is dedicated to bringing the security patches for the highly affecting vulnerabilities that were discovered in 2017. The incremental OTA is rolling out, which might take some time before it reaches every device worldwide. If you would like to update your device manually, then the instructions below will help you easily install ZTE Axon 7 B35 update unofficially using TWRP.
Page Contents
Download and Install ZTE Axon 7 B35 Update Unofficially
While Oreo for Axon 7 is still a work-in-progress, the company has decided to update the device to comply with the latest security norms. The announcement was made the official ZTE community for the A2017U variant in the U.S. The new build includes the December 2017 Security Patch that addresses the highly spread Blueborne and KRACK vulnerabilities on the device. The former is related to the Bluetooth functionality on the phone, while the latter is concerned with the WPA2 protocol. Both the vulnerabilities could be potentially used to inject malware and access personal data. It’s a relief for the users that the OEM is finally pushing out the update for fixes regarding the two.
Apart from above the ZTE Axon 7 B35 firmware also includes general bug fixes and improvements and is based on Android 7.1.1 Nougat. It is clearly stated to disregard the release notes mentioning that the Hiya app has been reverted back to 6.3.3.
Advertisement

As for the moment, the company has not made the firmware zip file available on the official servers. XDA senior member – DarkenFX has provided the system image files to help you install ZTE Axon 7 B35 Update right now. We appreciate the hard work that the XDA member has put into this and made it publically available for others. Users can make use of TWRP to flash the provided firmware files and update their device to the latest B35 firmware.
Requirements
- Take a complete backup of your personal data first. We suggest that you follow our guide on how to backup Android phones.
- Your device must have TWRP recovery installed. You can grab the latest recovery image from here and flash it using the command below.
fastboot flash recovery twrp-3.2.1-0-ailsa_ii.img
- Charge your ZTE device to at least 50-60% battery level to avoid shutdowns during the update process.
Once you have fulfilled the requirements stated above, read the instructions below to install ZTE Axon 7 B35 update right now.
Download ZTE Axon 7 B35 Firmware
How to Install ZTE Axon 7 B35 Update Unofficially
- Download the boot stack and stock system flashable zip files from above.
- Connect your Axon 7 to the PC using the USB cable.
- Transfer the downloaded files to the internal storage or SD card.
- Power down your phone completely.
- Press and hold the Volume Up and Power button altogether.
- As the ZTE logo appears, release the Power button and keep holding the Volume Up key to enter TWRP.
- In TWRP, go to ‘Wipe’ -> ‘Advanced Wipe’.
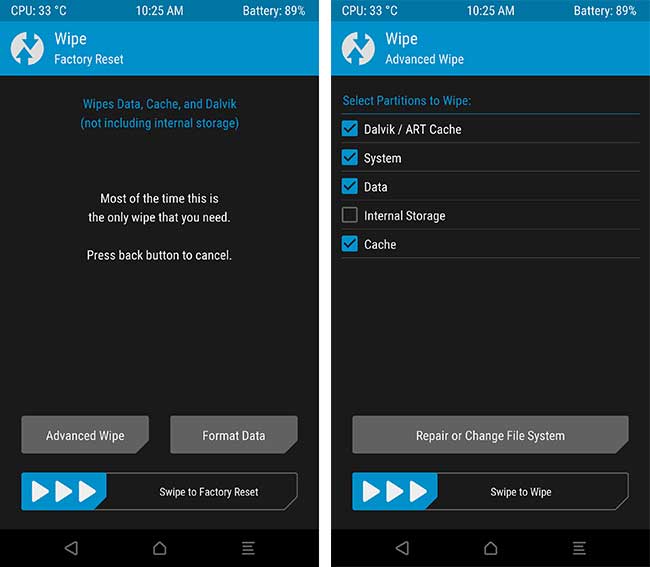
- Select the partitions as shown in the image and swipe the ‘Swipe to Wipe’ button.
- To install ZTE Axon 7 B35 update, go back to the TWRP main screen and tap on ‘Install’.
- Navigate to the storage and select the ‘A2017UV1.1.0B35_bootstack_by_DrakenFX.zip‘ file.
- Then swipe the button on the screen to flash the file.
- After the flashing process is complete, hit ‘Reboot System’.
Now that your device is updated, you can go ahead and enjoy a more secure firmware on your device. You can further root your device on the latest firmware using SuperSU. So this was how you can unofficially install ZTE Axon 7 B35 update. If you have any questions leave them down in the comments section below.
Source: XDA